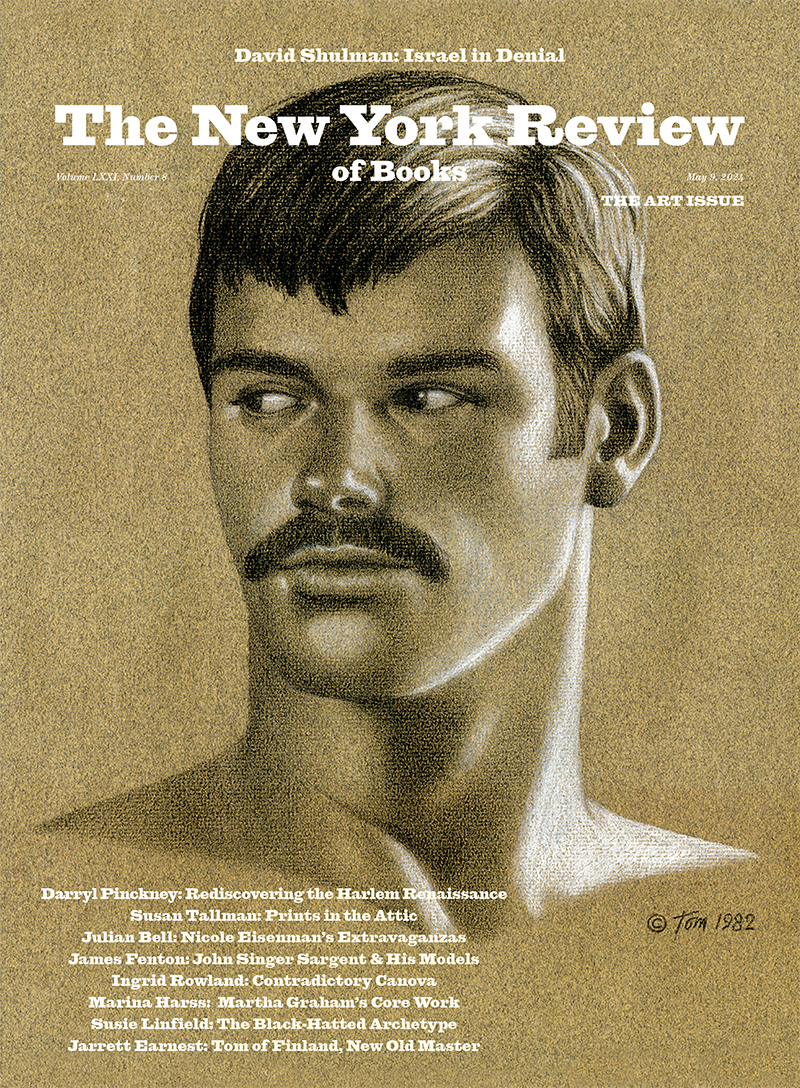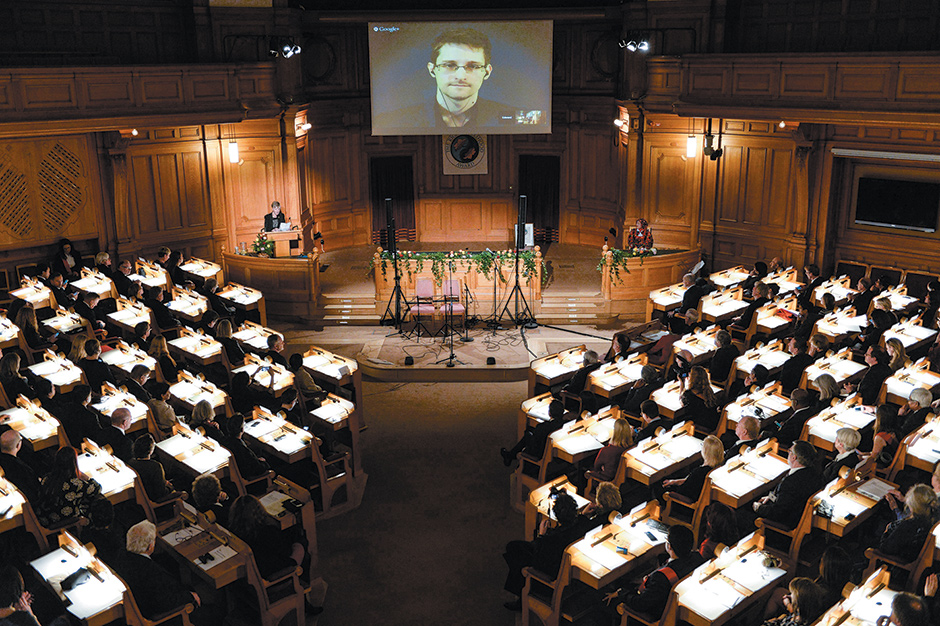
Pontus Lundahl/TT News Agency/Reuters
Edward Snowden, shown on a livestream from Moscow, receiving the Right Livelihood Honorary Award for ‘his courage and skill in revealing the unprecedented extent of state surveillance violating basic democratic processes and human rights,’ Swedish Parliament, Stockholm, December 2014
How did a constitutional law professor, vocal critic of President George W. Bush’s war on terror, and Nobel Peace Prize winner come to oversee an unprecedented campaign of secret targeted killing with drones, as well as the most extensive dragnet surveillance that the world has ever seen? While some have blamed President Barack Obama’s personal failings, and others have argued that these acts vindicate Bush’s policies, both explanations miss a deeper reality. These programs are best understood not as unique to Obama or Bush, or even the United States, but as reflections of how the world is changing in ways that threaten not only fundamental human rights to life and privacy, but the essence of democracy itself. As such, they raise questions that will not go away under this president or the next, but that will with increasing urgency confront nations around the world.
The drone and surveillance programs, like much of counterterrorism today, are driven principally by two phenomena: on the one hand, previously unthinkable terrorist threats, and on the other, equally unanticipated technological developments. These twin factors have motivated and enabled security agencies to undertake measures that were once impossible—and to do so in secret, without the awareness, much less approval, of the people on whose behalf they act.
Despite his criticisms of President Bush’s war on terror, Obama has maintained and even escalated some of Bush’s most controversial measures. Obama deserves credit for ending torture and shutting down the CIA’s secret prisons, in which, as the recently disclosed report of the Senate Select Committee on Intelligence (SSCI) shows, CIA agents and contractors subjected detainees to brutal, unconscionable, and illegal treatment. Obama attempted (albeit unsuccessfully) to close Guantánamo. But he has also sharply increased remote-controlled killings of suspected terrorists. According to the New America Foundation, President Bush launched forty-nine drone strikes, but Obama more than 440. They have been used in Yemen, Somalia, and Pakistan, countries with which we are not at war, often far from any battlefield. And the strikes have been used to kill many persons who were not at the time of their deaths engaged in any imminent hostilities against us.
According to one inside account, the US drone “kill list” was reviewed on weekly conference calls with as many as one hundred government officials, a procedure that only Ambrose Bierce, author of The Devil’s Dictionary, would call due process. The attacks are approved and carried out in secret, and not acknowledged even after the fact. For much of Obama’s term, the criteria for selecting targets and the process employed were both obscure. For years, the US did not even admit that such a program existed. Today, there is more transparency about the general rules, but still almost none about how the rules are applied in individual cases.
As Steve Coll has recently shown, there is substantial dispute about every aspect of the US drone war in Pakistan, including who has been targeted and on what basis, how many innocent victims have been killed or wounded, and whether the Pakistani government approved of all or some of the strikes.1 The result, reports Coll, has been widespread resentment against the US tactic.
Meanwhile, the National Security Agency (NSA), often acting with Britain’s Government Communications Headquarters (GCHQ), has conducted an international dragnet surveillance program of unprecedented scope. That nations spy on suspects in other countries is hardly news. But Edward Snowden’s disclosures showed that the NSA and the GCHQ have been collecting billions of electronic communications—including the contents of phone calls, cell phone location data, texts, e-mails, chats, and contact lists—from wide swaths of people under no suspicion whatsoever.
In one example, the NSA has been recording the contents of every single phone call made in an undisclosed country, and has the capacity to review retroactively the contents of any call. At home, the NSA has been collecting metadata on virtually every American’s every phone call—in this instance, not the content, but who you called, when you called, and how long you talked. For several years, it collected similar data on virtually every American’s Internet communications. And both the NSA and the GCHQ acted entirely in secret; the people had no say in whether these programs should exist.
The drone and surveillance programs are a function not so much of Obama or Bush (or, in the UK, Blair or Cameron), but of two related phenomena: the new terrorist threat and digital technology. The US, the UK, and many other states now face threats from nonstate actors eager to engage in acts as depraved as the attacks of September 11, 2001, and July 7, 2005, or the recent videotaped beheadings of British and American hostages. These groups have the capacity to plan and stage their attacks from afar, often from barely governed regions. Among them are people ready to sacrifice their own lives to inflict terror. As one former US official described it, defending against such threats is like playing goalie blindfolded, where the opposing side can score from in front, behind, above, or below.
Advertisement
At the same time, technology has rapidly evolved, making previously unthinkable government security undertakings entirely feasible. Digital technology has radically reduced the practical obstacles that we used to rely on to protect our rights as much as if not more than we relied on formal law. Twenty years ago, if the US learned that someone in Yemen was plotting terrorist attacks against its interests, it could work with the Yemenis to monitor and arrest him. In extraordinary circumstances, it could send a cruise missile or special operations forces into his village in hopes of killing or maiming him, but at substantial risk to the lives of others. Yemen would not likely consent to a cruise missile attack or small-scale invasion, so sovereignty concerns would also deter us. Today, the US can send an unmanned drone to bomb a relatively precise target at a precise time, requiring no troops on the ground, limiting collateral damage, and providing a greater degree of plausible deniability.
Intelligence gathering and investigation have also radically changed. Twenty years ago, if the government wanted to know your most intimate secrets, it could seek to follow you around the clock. But that is very expensive and difficult, and could practically be deployed only against very high-priority suspects. It could search your home, but only if it first obtained a judicial warrant based on specific probable cause. It could interrogate you, but only if it had probable cause to arrest, and even then, you could assert your right to remain silent.
Today, the government can simply go to the various electronic communications service providers you use and obtain from them detailed information on your every phone call, Web search, e-mail, online chat, or credit card purchase, as well as your physical location whenever you are carrying your cell phone. Under current law, you have no constitutional right to object to the government obtaining the information from the companies that serve you. The government needs no probable cause or warrant to get it.
And this information tells more about you than your closest family and friends know, more even than you yourself know. I forget what I was doing, where I was going, and what I was thinking about three months ago—but my smartphone, computer, and Internet account have it all recorded, in convenient, computer-searchable form. So it’s now possible to obtain a detailed, intimate portrait of anyone at low cost, without any basis for suspicion.
The digital age also makes possible dragnet surveillance of whole communities. Twenty years ago, no government could monitor all phone calls from a single country or secretly collect the personal address books of millions of individuals. The computers were not fast enough, the hard drives not big enough, the algorithms not sophisticated enough, the world not linked enough. Today, mass collection and analysis are conducted every day by Google, Yahoo, British Telecom, and many websites. And as the NSA and the GCHQ have shown, government agencies can obtain that information from the private sector virtually at will.
The logic of the security state is simple. Those in charge of security, whether at the NSA, the CIA, MI5, or other agencies, know that if a terrorist attack occurs, and it turns out they could have monitored the killers or eliminated them with a drone, but chose not to do so, the recriminations will be loud. Security agencies are driven by the imperative of prevention to deploy these tools to their maximum potential. In the words of an NSA PowerPoint slide disclosed by Snowden, the agency’s goal is to “Collect It All,” “Process It All,” “Exploit It All,” “Partner It All,” “Sniff It All,” and “Know It All.”
Until recently, practical obstacles to mass surveillance and long-distance killing almost certainly were more effective in preserving privacy, and limiting nations’ resort to force, than formal laws and legal institutions. Now that technology has sharply reduced those obstacles, there’s an urgent need to fill the gap with other constraints—in the form of law, oversight, and accountability. Yet adequate forms of control have yet to emerge.
Surveillance and targeted killing are not per se unlawful. They are unlike torture, which is absolutely forbidden under all circumstances. Properly regulated, surveillance is a legitimate governmental function in peacetime and wartime. Every country does it; no country forbids it. Privacy is an important and valuable right, but it is not absolute.
Advertisement
Similarly, state killing is sometimes legal. In peacetime, police may use deadly force under narrowly circumscribed conditions—in the United States, for example, when a suspected felon is fleeing, won’t halt, and poses a threat of death or serious bodily injury to others. In war, one can generally kill the other side’s soldiers unless they have surrendered or been captured. And even outside of an ongoing conflict, if someone poses an imminent threat to the nation that cannot be curtailed through other means, the nation may use lethal force as a last resort in self-defense.
The new technologies of surveillance and killing, however, raise many novel and difficult questions. For example, should the government be permitted to collect huge amounts of private information if there are strict limits on how and when it can be looked at and used? Our law, by regulating searches, has traditionally limited the police’s ability to collect private information. But once a search is done, there is little or no restriction on how the information is analyzed or used. Now that so much data is collected virtually automatically by the private sector, do we not have to focus on regulating use as well as collection?
The dangers of broad-based collection and surveillance are not hypothetical. The Framers of the US Constitution drafted the Fourth Amendment specifically to prohibit the Crown’s misuse of “general warrants” to search indiscriminately. In the 1960s and 1970s, the FBI used the asserted threat of “communist infiltration” to spy on civil rights leaders such as Dr. Martin Luther King. In August 2013, The Wall Street Journal reported that some NSA officials abused their authority to track their ex-wives or girlfriends. And documents disclosed by Snowden showed that the NSA and the FBI monitored Muslim civil rights leaders in the US—without any apparent basis for suspecting them of terrorism.
Targeted killing, whether by drones or other means, also presents real risks and new questions. While the numbers are disputed, there is no doubt that many innocent civilians have been killed. According to the New America Foundation, in Pakistan alone, between 250 and 300 civilians have been killed. No matter how precise the targeting technology, a strike is only as accurate as the intelligence upon which it is based. In December 2013, a US drone strike reportedly killed at least eleven members of a wedding party in Yemen. What we do today is a precedent for what others will do tomorrow. How would we feel if, instead of the US and the UK deploying drones to kill overseas, China were killing “terror suspects” in Taiwan, or Pakistan were targeting enemies in India?
Drone killings and NSA and GCHQ surveillance are not necessarily illegal under US or international law, but they undoubtedly raise serious questions demanding an intensive public debate. Here’s the difficulty. The same phenomena I noted at the outset—the new character of the terrorist threat and advanced digital technology—have also increased dramatically the extent to which governments can and do conduct their activities in secret.
There used to be practical limits on what governments could keep secret or plausibly deny. In the old days, if the government sought to follow an individual’s every move, thought, and action, there was a high likelihood that he would learn he was being followed. If the government wanted to monitor entire communities, it would be virtually impossible to keep that activity secret. And once such actions were made public, they would likely set off a political reaction, as when the nation learned that J. Edgar Hoover was spying on civil rights and peace groups in the 1960s.
It was similarly difficult to conduct extensive surveillance overseas without being discovered. Today, however, the NSA or the GCHQ can tap into an Internet service provider’s trunk line and immediately gain access to records on millions of people without their knowledge.
Similarly, because drones are capable of being used discriminately, and are largely invisible until they strike, the identity of those controlling them can be denied in ways that more traditional uses of force cannot. Yemen and Pakistan both reportedly allowed the US to conduct drone strikes in their territories on the condition that the US not acknowledge that it was doing so. No government wants to tell its people that it has permitted another country to conduct remote-control killings of its own citizens within its borders. Deniability was critical to the agreements. The killings, so the governments thought, had to be secret. And drone technology made that possible.
At the same time, the fact that terrorists operate clandestinely, may strike at any time, and use global telecommunications to coordinate attacks causes states to monitor more extensively, and to keep their monitoring tactics secret to increase their effectiveness.
As has often been said, sunlight is the best disinfectant. Because secrecy has been so central to these programs, transparency makes a critical difference in how they are conducted. All drone-monitoring groups agree that the number of drone strikes and the ratio of reported civilian casualties fell dramatically as the US became more transparent about its use of remotely controlled weapons.2
With respect to the NSA’s domestic phone surveillance, all three branches of the US government changed their tune once Snowden disclosed the program. One of the government’s most frequent defenses of the program was that all three branches had approved it. But that was true only as long as the program remained under wraps. Once it became public, President Obama, who had allowed the program to continue in the form his predecessor had left it, appointed an expert review panel, and endorsed several of the reforms it suggested. He agreed, for example, that the NSA should be required to obtain judicial approval before every search of its telephone database; that those searches should be more limited in scope; and that a public advocate should participate in hearings before the Foreign Intelligence Surveillance Court. Another executive branch body, the Privacy and Civil Liberties Oversight Board, launched an investigation and determined that the domestic telephone metadata program was unauthorized by statute.
The courts, which had repeatedly authorized the NSA’s domestic phone metadata program while it was secret, also changed their approach once it became public. A federal district court in Washington, D.C., declared that the program was likely unconstitutional. The Foreign Intelligence Surveillance Court itself, which had routinely rubber-stamped the official collection of metadata while it was secret, without even writing an opinion explaining its reasoning, wrote an opinion to explain its rationale only after the program was publicly revealed. And that court, which previously kept all its opinions secret, has now released many of its opinions so that they can be publicly assessed.
Congress, which had repeatedly reauthorized the USA Patriot Act provision that the NSA relied on to conduct its domestic phone data program, also altered course once the program was public. The House of Representatives overwhelmingly passed the USA Freedom Act, a bill designed to rein in the NSA by, among other changes, authorizing more limited access to phone metadata and allowing privacy advocates to participate in Foreign Intelligence Surveillance Court hearings. Senator Pat Leahy improved the bill in the Senate, and obtained agreement from the administration to further reforms. These included ending bulk collection of phone data, requiring judicial review before any phone data is demanded, and imposing tougher reporting requirements.
In a major disappointment for privacy advocates, that bill fell two votes shy of the sixty needed to overcome a filibuster in the Senate’s lame-duck session. Some of the objecting senators felt the reforms did not go far enough, but others were reluctant to tie the NSA’s hands too tightly in light of recent threats, such as ISIS—even though the executive branch said it could operate effectively under the proposed reforms. But there was still a bipartisan majority for reform.
The new Senate will be less sensitive to civil liberties. Mitch McConnell, the new Senate leader, is an ardent opponent of NSA reform, as is Charles Grassley, who will succeed Leahy as chair of the Senate Judiciary Committee. But the statute upon which the phone metadata program rests expires in June 2015, so reformers will be in a position to demand meaningful limits as the price of extension. The Republicans will have to agree to some reforms if they want the authority to continue.
Disclosures about NSA spying have also changed the actions of Silicon Valley corporations, major forces in the surveillance debate, both because the government needs their cooperation and because they are a substantial part of the US economy. Their business interests have been hurt by the worldwide perception that they were going along with, or at least were too easily exploited by, the NSA. So they are now squarely behind privacy reforms. That, too, offers hope for the future.
Transparency about new technology is essential for three reasons. First, it is necessary to hold governments accountable. How are the governments in Yemen and Pakistan accountable if they secretly let the US conduct drone strikes only on the condition that the US not acknowledge it is doing so? How was the NSA phone metadata program legitimate if the American people didn’t know about it?
Second, transparency is necessary if we are to have any chance of restraining the national security–industrial complex. The US spent $3.3 trillion on counterterrorism in the first decade after September 11. There are forty-six separate national security agencies. Some 854,000 people have security clearances from the US government. Private technology and security companies, which land huge government contracts to develop and operate better surveillance tools, have become one of the nation’s most lucrative industries. As a result, substantial institutional forces will press for expanded security authorities, and will seek to create ever more powerful ways to monitor human activity. As the SSCI’s recent torture report illustrates, security agencies will, if they can, systematically lie and mislead to cover up their abuses and errors. As long as their programs remain hidden, we have no hope of checking them.
Finally, transparency is important to the government. If it keeps programs of this nature secret, the public will understandably fear the worst. The long-unacknowledged drone killing program led many people to believe that the US claimed the power to kill anyone, anywhere, without process or standards. As the Obama administration began to explain its drone policy, it became clear that it did not take such a capacious view of its authority. The president has said that targeted killing away from a conventional battlefield is limited to imminent threats who cannot be captured or otherwise countered, and will be undertaken only where the risk of civilian casualties is virtually nil. But as long as the program and its contours were secret, people lacked clear reasons not to fear the worst. For these reasons, Sir David Omand, former head of GCHQ, has recently recommended greater transparency about the UK’s policy on drones and intelligence sharing precisely because candor is necessary to counter misinformed opposition and legitimize drones’ beneficial uses.
In response to recent announcements that Apple and Google have built into their new cell phones a default encryption that the companies themselves cannot decode, FBI Director James Comey and GCHQ head Robert Hannigan have expressed concern that important information will not be available and called for public debate on terrorism and technology. It is disappointing, if not surprising, that they see a need for public debate only when new technologies may impair their ability to monitor us, and not when such technologies enhance their monitoring. A public debate is needed, but it cannot proceed without the kind of transparency that thus far the security agencies have obdurately resisted.
Of course, transparency has costs as well as benefits, and secrecy is sometimes necessary. But secrecy has significant costs, too—not just to human rights, but to democracy itself. As US Court of Appeals Judge Damon Keith warned in 2002, in a case involving secret immigration trials, “Democracy dies behind closed doors.” We won’t have a chance to arrive at defensible policies on surveillance and targeted killing if the questions are not fully and fairly debated. When the balance between individual rights and security is struck in secret one-sided determination, as has been the case with both drone killing and electronic surveillance, as well as the CIA’s enhanced interrogation program, it will inevitably be skewed.
Increasingly, our governments seem to be insisting that our lives be transparent to them, while their policies remain hidden from us. For the sake of democracy itself, we must do all we can to resist that impulse.
—December 10, 2014
This Issue
January 8, 2015
In Ferguson
A Better Way Out
Who Is Not Guilty of This Vice?