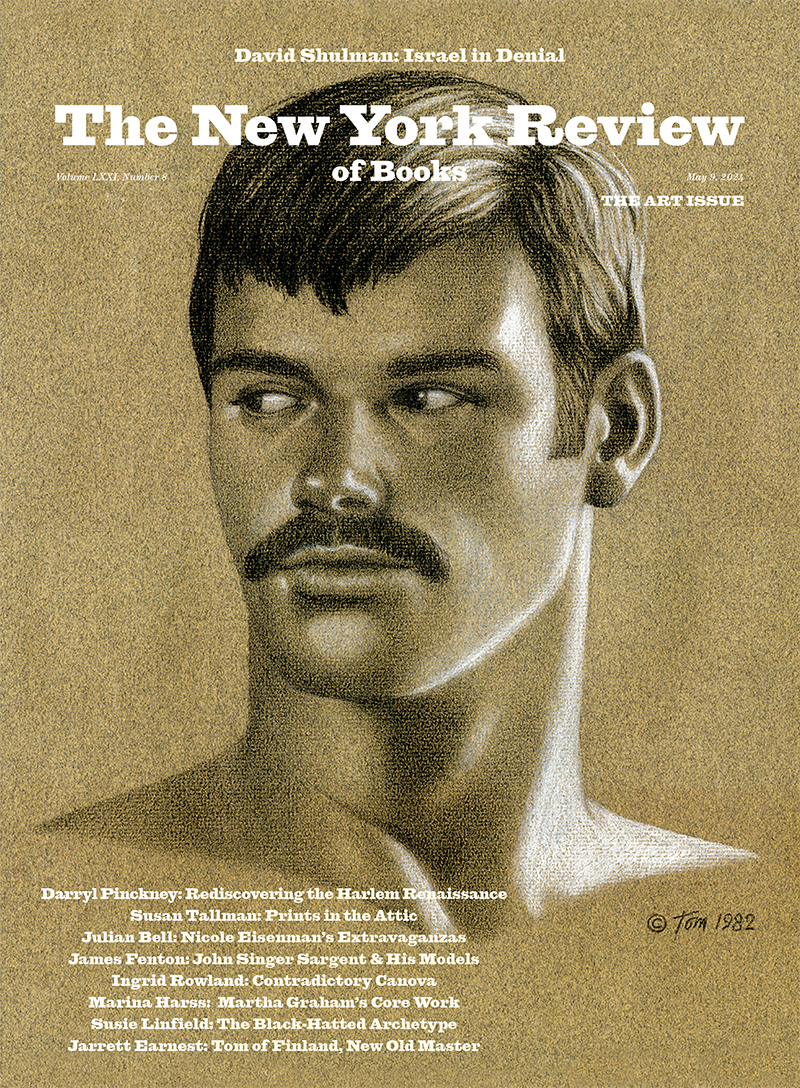
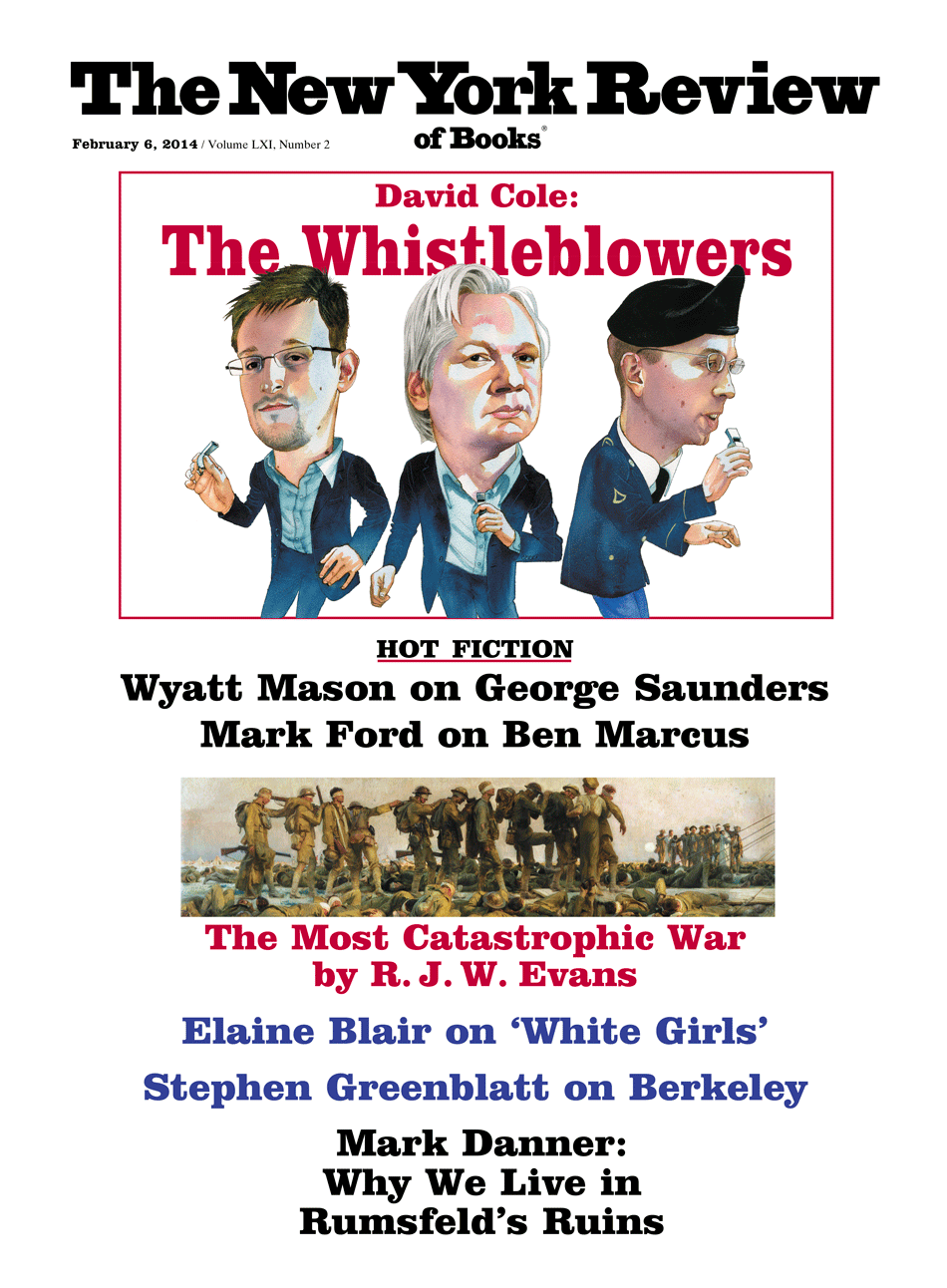
What should we make of Edward Snowden, Bradley (now Chelsea) Manning, and Julian Assange? Their names are known across the globe, yet the actions that made them famous have also driven them to lives of intense isolation—in hiding, in prison, or in a foreign embassy. They have been lionized as heroes and condemned as traitors. Snowden, a former contractor for the National Security Agency (NSA), and Manning, a low-level army intelligence analyst, are responsible for the two largest unauthorized disclosures of classified information in the nation’s history.
Manning released to Assange’s website, WikiLeaks, about 720,000 secret documents from the State and Defense Departments, and Assange published them on the Internet. The NSA still doesn’t know the full extent of the information Snowden stole and passed on to the journalists Glenn Greenwald, Laura Poitras, and Barton Gellman, but it estimates the number to be 1.7 million classified documents, concerning some of the US’s most closely guarded secret surveillance programs.
The federal government views Manning and Snowden as criminals. It tried and convicted Manning for violating the Espionage Act and he was sentenced to thirty-five years in prison. (Manning subsequently announced that he was changing his gender, and hereafter would be known as Chelsea.) The government has charged Snowden with stealing government property and violating the Espionage Act, although he has thus far evaded trial by obtaining temporary asylum in Russia. And the Justice Department has empaneled a grand jury to investigate Assange, who is holed up in the Ecuadorean embassy in London seeking to evade extradition to Sweden for alleged sex crimes.
The prosecutors in Manning’s trial repeatedly contended that Assange actively encouraged Manning’s crimes. In November, however, a Justice Department official told the The Washington Post that Assange would not likely be prosecuted for publishing Manning’s documents. According to former Justice Department spokesman Matthew Miller, “if you are not going to prosecute journalists for publishing classified information, which the department is not, then there is no way to prosecute Assange.” But the grand jury investigation continues.
Others praise Manning, Snowden, and Assange for exposing our government’s secret and legally dubious activities at home and abroad. Snowden’s revelations about the scope of NSA electronic surveillance have touched off a much-needed national and global debate about privacy in the digital age. Indeed, because of his influence he was rumored to have been the runner-up to Pope Francis for Time magazine’s “Person of the Year.” Manning’s and Assange’s disclosures had much less dramatic effect, but they, too, revealed a host of potential abuses, including US troops in Iraq killing civilians, the US State Department spying on foreign UN officials, and a secret agreement between Yemen and the United States to permit US drone strikes there on the condition that they not be publicly admitted.
These leaks, the most significant since Daniel Ellsberg made the Pentagon Papers available to The New York Times and The Washington Post in 1971, raise anew the question of when it is justified to disclose classified information to the public. Some advocates of transparency seem to treat any exposure of secrets as an unmitigated good; this appears to be the philosophy behind Assange’s WikiLeaks. But that position is morally untenable; there are undoubtedly good reasons for secrecy in many aspects of government, especially foreign relations, and particularly during wartime. And there are many legitimate bases for condemning disclosures, particularly when they reveal the identities of sources and methods of foreign intelligence.
Security hawks consider any unauthorized disclosure of classified information unacceptable, stressing that cleared employees take an oath not to disclose such information, and that no government can operate without some secret deliberations and covert actions. But this, too, is an untenably extreme position. History demonstrates that secrecy is used not only for legitimate purposes of national security, but too often to shield illegal or embarrassing activity from public scrutiny. Even the most ardent security proponent must concede that the benefits from revealing illegal abuses of authority will sometimes outweigh the costs of disclosing those secrets.
If neither extreme is acceptable, how should we distinguish legitimate from illegitimate leaks? The Intelligence Community Whistleblower Protection Act, passed in 1998, marks one effort at striking a balance. It provides a way for individuals to disclose classified information regarding a “serious or flagrant problem, abuse, violation of law,” but only to members of congressional intelligence committees, and only after initially presenting it to the NSA’s inspector general and the attorney general. This law, however, provides no protection for revealing information to the public, and has been used only rarely. Whatever balance it struck in theory has proven largely irrelevant in practice.
To understand why, imagine if Snowden had gone to the NSA’s inspector general with information that the agency was collecting large amounts of “metadata” on every American’s phone calls—i.e., records of who they called, when, and for how long they talked—storing the data for five years, and searching through it. What would the inspector general have done? As the NSA’s defenders repeatedly emphasize, the metadata program was blessed by all three branches. The Bush administration instituted it and Obama maintained it. Fifteen federal judges on the secret Foreign Intelligence Surveillance Court—or FISA court—declared it lawful. And Congress reauthorized the Patriot Act provision upon which the program was based, even after being informed of the program (albeit in a limited and anodyne manner designed not to raise any alarms).1
Advertisement
Given these circumstances, the inspector general surely would have responded that there was no basis for disclosing it. But even if Snowden had been given a green light to bring the NSA’s activities to the attention of the intelligence committees, the problem was not that those committees were in the dark, but that the American people were. As Snowden put it in a videotaped interview from Hong Kong at the time of his initial leaks, “These things need to be determined by the public, not by somebody who was simply hired by the government…. The public needs to decide whether these programs and policies are right or wrong.”
The reactions that Snowden’s disclosures have sparked suggest that he was onto something. The only parties kept out of the “checks and balances” so often lauded by the NSA’s defenders were the American and global publics—in other words, the people whose privacy was at stake. As long as the program was kept under wraps, all three branches of government were willing to tolerate it. But once it became public, that changed dramatically. On December 16, the first federal court to assess the legality of the NSA’s telephony metadata program in a public, adversarial proceeding declared it likely unconstitutional. US District Judge Richard Leon ruled that the mass collection and search of metadata invaded US citizens’ reasonable expectations of privacy, and could not be justified without a warrant and probable cause.2
Two days later, the president’s own expert panel, which included a former acting director of the CIA, raised serious questions about the wisdom and propriety of the program, and recommended forty-six reforms to rein in the NSA, including an end to the NSA’s bulk collection of telephone records, more judicial and legislative oversight, and a requirement of specific presidential approval for spying on foreign leaders.
Members of Congress have introduced more than thirty bills to restrict the NSA. The most important bill is cosponsored by Jim Sensenbrenner, a Republican from Wisconsin in his thirty-fifth year in Congress, and Senator Patrick Leahy, the veteran Democrat from Vermont. Sensenbrenner, an architect of the original Patriot Act, says that he never imagined that it could authorize what the NSA has been doing. And Silicon Valley is also urging reforms, arguing that the NSA’s practices have not only damaged privacy, but undermined their businesses—and the US economy—by eroding trust in the confidentiality of US-based Internet services.
At the end of December, US District Judge William Pauley III in Manhattan, disagreeing with Judge Leon, ruled that the NSA’s program was constitutional. Judge Pauley reasoned that Americans have no legitimate expectation of privacy in the phone numbers they call, and therefore have no constitutional basis for objecting to the NSA’s mass collection and searching of that data. If an appeals court finds the NSA program unconstitutional, review by the Supreme Court is almost certain.
In the end, the Obama administration, Congress, and the courts should all act to curb NSA spying. More targeted surveillance, subject to closer judicial oversight, should replace the NSA’s current dragnet approach. How the conflict ultimately will be resolved will not be known for some time. But one thing is clear: none of this debate would have happened without Snowden’s revelations.
Consider what we have learned from Snowden’s leaks and the further government disclosures that they prompted:
(1) Since 2006, the NSA has been systematically collecting records on every phone call every American makes. It has done so on the basis of NSA lawyers’ secret, strained interpretation of a Patriotic Act provision that authorized the collection only of records “relevant” to an investigation of international terrorism. The NSA argued that it can collect everyone’s phone records, regardless of any connection to terrorism, on the theory that the records might in the future become “relevant” to a terrorism investigation. But on that theory, what records couldn’t the NSA collect?
(2) Director of National Intelligence James Clapper lied under oath about this program when asked in a congressional hearing whether the government was collecting any kind of data on millions of Americans. Clapper answered “no,” but Snowden has shown that the NSA was doing precisely that.
Advertisement
(3) Under another statute, the FISA Amendments Act of 2008, the NSA has engaged in far more intrusive surveillance—including reviewing the content of e-mails, Internet searches, and chat rooms—of persons it believes are foreign nationals overseas, even if they are communicating with US citizens here. It may do so without any individualized suspicion that the target is engaged in criminal or terrorist activity. The agency has tapped the phones and e-mails of some of our closest allies’ leaders, including German Chancellor Angela Merkel and Israeli Prime Minister Ehud Olmert.
(4) These NSA programs were authorized in secret by FISA judges, but have often violated the terms under which the courts authorized them. For example, in 2009 FISA Judge Reggie Walton castigated the NSA for illegally reviewing thousands of Americans’ phone data over two years, and imposed a temporary requirement (later lifted) that all searches of the database be preceded by judicial approval.3
(5) Within the United States, the NSA has been collecting not just records of Americans’ phone calls, but of their e-mails as well. E-mail data is often even more revealing than phone data (identifying, for example, the e-mail groups and political and religious organizations with which one communicates).
(6) The NSA has been collecting cell phone location data and e-mail address lists from outside the US on a vast scale, data that tracks phone users’ every move around the clock and reveals e-mailers’ closest associations.
(7) The NSA has not been satisfied even with all of these powers. It has hacked into the overseas links between Google’s and Yahoo’s data hubs, vacuuming up enormous amounts of data, subject to no statutory or judicial limits whatsoever. And it has inserted vulnerabilities into private industry’s encryption codes to enable it to hack into them more easily.
(8) Finally (at least for now), the NSA has been cooperating in potentially disturbing ways with its British counterpart, Government Communications Headquarters (GCHQ), apparently exploiting loopholes that allow the NSA to do things GCHQ could not, and vice versa.
And Snowden is not done yet. Reports of new programs, initiatives, and targets break weekly if not daily. In short, Snowden’s disclosures portray an insatiable agency that has sought to collect as much information as it possibly can, most of it relying on secret interpretations of law, often exploiting the fact that the law has not caught up to technology.
Were Snowden’s leaks justified? Rahul Sagar’s Secrets and Leaks sheds important light on the question. In carefully argued and lucid prose, Sagar, a professor of politics at Princeton, argues that secrets are inevitable, as are leaks—and that leaks have an important if precarious part in checking secrecy abuse. The power to declare information secret, like many other authorities, is both essential and susceptible to misuse. In theory, formal legal checks on executive power to determine what should and should not be secret would be preferable to leaving abuse-checking to leakers who take it upon themselves to break the law. But, Sagar contends, the two principal alternative candidates for implementing formal oversight—the courts and Congress—are each unlikely to perform the function effectively.
Courts, Sagar argues, are not well positioned to second-guess executive assessments that particular information must remain secret, save in the most egregious circumstances. Judicial practice bears him out; courts generally defer when the executive contends that national security requires secrecy. For its part, Congress is simply too large, porous, and partisan to be entrusted with the job. And whichever branch of government undertakes this checking function will have to do its work in secret, and thus will face some of the same temptations and credibility problems that the executive does.
Moreover, the question of when a leak is justified is not generally susceptible to resolution by clear rules set out in advance. The disclosure of a flagrant criminal act might seem to be an easy case, but most leaks don’t involve flagrant criminality. Nothing disclosed by Snowden or Manning, for example, rises to that level. And it is conceivable that even in the case of a clear crime, the damage to national security from disclosure might outweigh the benefits—as where revealing a minor crime would blow the cover of important clandestine agents.
Sagar is not a naive defender of leakers, however. He recognizes that there are real risks when unelected individuals transgress judgments of elected leaders on matters of the nation’s security. They may act for personal or partisan reasons and expose information in one-sided and misleading ways that are difficult for the government to counter without spilling still more secrets. They often do not have the information or perspective to assess accurately the potential damage from their disclosures. And as self-appointed guardians, they lack democratic legitimacy.
Nonetheless, Sagar argues that disclosure of secrets by private leakers is morally justified when it (1) is based on clear and convincing evidence of abuse of public authority, (2) does not pose a disproportionate threat to public safety, and (3) is as limited in scope and scale as possible. Sagar has helpfully identified the right questions. But as he himself is the first to concede, the application of these principles in individual cases is extraordinarily difficult.
By Sagar’s standards, Manning’s and Assange’s disclosures were for the most part not justified. While some specific war logs and cables may have revealed illegal conduct without disproportionate harm to public safety, Manning’s dump of several hundred thousand documents was in no way narrowly tailored. The leaked State Department cables in particular “outed” many individuals who put themselves at considerable risk by confiding in embassy officials in countries with repressive regimes or internal strife.
Manning’s disclosures forced the US to devote vast resources and time attempting to identify persons at risk and help secure their safety. Manning’s defenders object that the government has not named anyone who was actually killed as a result of the disclosures, but that may well be a combination of quick responses and sheer luck. And even if no one was killed, the disclosures reduced the reliability of US diplomats’ promises of confidentiality, and thereby almost certainly deterred others from coming forward. Much like journalism, diplomacy depends for its lifeblood on promises of confidentiality. In any event, there is no evidence that Manning made the kind of fine-tuned assessment that would have justified disclosures—or that he had the knowledge to do so.
The ethical and legal questions for Assange, as for journalists generally, are different. Manning was afforded access to classified information on the specific condition that he not disclose it. Assange, an Australian freelance journalist and publisher, was under no such obligation. Because of the protection given to journalists by the First Amendment, no member of the press has ever been prosecuted under the Espionage Act for publishing classified information. Thus, while Manning serves thirty-five years and Snowden faces even more serious penalties, the journalists who published their leaks are generally free from prosecution.
Still, while journalists who obtain classified information generally have no legal duty to keep it secret, they have an ethical obligation to consider the risks that their reporting may create. Contrary to some reports, WikiLeaks did initially take measures to “redact,” or black out, the names of individuals who might be put at risk from its publication of Manning’s documents. But it also made the unredacted documents available to some journalists, subject to a not very carefully controlled password, and when a Guardian journalist published the password, WikiLeaks in turn published the cables in their unredacted entirety. The result is that thousands of cables were published that disclosed no violations of law, many of which put innocent individuals at risk of retaliation.
Snowden’s is a more complicated case. Did he have “clear and convincing evidence” of an “abuse of public authority,” as Sagar would demand?
The most significant abuse of authority that Snowden has revealed is not the illegality of any particular NSA action, but the fact that such an extensive spying program was authorized entirely in secret, without public input, assent, or even knowledge. While there must be room in a democracy for limited covert actions, surveillance of this scope—affecting every American and large swaths of the world’s citizenry—should not be instituted without public acceptance and accountability. And in an increasingly globally interconnected world, the legitimacy of the NSA’s actions cannot be determined solely by the American people. If the NSA is indeed collecting comprehensive data on the lives of millions of innocent foreign nationals, they, too, should have a voice in how they are being treated.
Snowden’s disclosure put an end, in the most dramatic way possible, to the secrecy that was, for him and many others, the central abuse of the program. For that reason, he recently told The Washington Post that he considers his mission accomplished.4 Thanks to Snowden, we can now have the debate that we should have had long ago, and that we will need to continue to have as advances in technology give the government greater power to track at low cost the most intimate details of all of our lives. That is a substantial benefit.
As for costs, disclosing the details of the NSA programs may give terrorists a better chance to evade detection. It’s not clear, however, how much of a cost that really is: terrorists already had to assume that they could be under surveillance. Even under the government’s long publicly acknowledged surveillance power, it could tap the phones and obtain business, phone, and Internet records about persons it suspected of involvement in international terrorism. A terrorist cannot know how much the government suspects about him, and therefore must assume he is being monitored.
Perhaps most important, it remains to be seen whether Snowden’s disclosures were narrowly tailored to abuses. We don’t yet know how many documents he has shared with the media. If in fact he took and disclosed 1.7 million documents, one would be hard-pressed to call his actions narrowly tailored. On the other hand, the various stories that have thus far been published seem to have been carefully circumscribed; they are very different from the Manning-Assange undifferentiated dump.
The New York Times has called on the government to grant Snowden “a plea bargain or some form of clemency” in light of the substantial good his disclosures have done. Rick Ledgett, the NSA official in charge of assessing Snowden’s disclosures, has also suggested a deal in exchange for Snowden returning the remainder of the documents. There is a strong case that many of Snowden’s leaks to date have been justified. Future disclosures, however, may do more harm than good, so it would be in everyone’s interest to reach a resolution that falls well short of the harsh punishment that most intelligence officials have thus far demanded. Snowden has committed serious crimes, but he has also performed a considerable public service.
The question of the legitimacy of leaks is not new, of course. Ellsberg’s disclosure of the Pentagon Papers more than forty years ago prompted similar questions. James Goodale, who as general counsel for The New York Times courageously advised publication of the Pentagon Papers, has recently published a fascinating inside story of the Times’s legal battles against censorship. In a coda, Goodale portrays Manning and WikiLeaks as modern-day manifestations of Ellsberg and the Times, and insists that freedom of the press has as much to fear from Obama as it did from Nixon. Some of Goodale’s parallels are apt, but the differences between the cases are more telling.
First, unlike Nixon, Obama did not attempt to prohibit the publication of any of Snowden’s or Manning’s leaks. The Pentagon Papers case, thanks in part to Goodale’s own arguments before the courts, established an extraordinarily high legal bar for enjoining publication, and that bar holds today. For many of the justices in the Pentagon Papers case, however, that bar applied only to “prior restraints”—requests to prohibit publication altogether—and would not apply to after-the-fact criminal prosecutions of leakers. While the Times was not prosecuted, Ellsberg was, and his case was dismissed not on First Amendment grounds, but on the basis of prosecutorial misconduct.
Second, the digital age has profoundly altered the dynamics and stakes of leaks. Computers make stealing documents much more efficient. Ellsberg had to spend months manually photocopying the Pentagon Papers. Manning used his computer to download over 700,000 documents, and Snowden apparently stole even more. The Internet makes disclosures across national borders much easier. Manning uploaded his documents directly to WikiLeaks’ website, hosted in Sweden, far beyond US reach. Snowden gave access to his documents to journalists in Germany, Brazil, and the US, and they have in turn published them in newspapers throughout the world.
Third, computers and the Internet have at the same time made it easier to identify and prosecute leakers. When someone leaked the fact that the US had placed an agent inside an active al-Qaeda cell in May 2012, an entirely unjustifiable disclosure, the Justice Department spent eight months investigating the old-fashioned way, interviewing over 550 people without success. But when the prosecutors subpoenaed phone records of the Associated Press offices and reporters involved in publishing the story, they promptly identified the leaker, an FBI agent, and obtained a guilty plea.
Free press advocates complain that the Obama administration has brought more prosecutions under the Espionage Act for leaks (seven) than all previous administrations combined (three). But the most telling fact is not that Obama has been more active, but that these numbers are so low, in view of the almost daily leaks of classified information published by the press. The increased prosecutions under Obama more likely reflect the fact that it is much easier to pinpoint the source of a leak than that President Obama cares little for press freedom.
One thing has not changed from the days of the Pentagon Papers. There is still no good systematic way to regulate government secrecy. As a result, secret abuses are an ever-present risk—as are leakers themselves. But precisely for that reason, leakers perform a critical, if troubled, function in deterring secrecy’s misuse. Executive officials must act with the knowledge that even their most secret conduct may someday be made public. President Obama’s expert panel recommended a “front-page rule,” by which the government would undertake in secret only those programs that it could defend if they appeared on the front pages of the nation’s newspapers. They may well have no choice in the matter. If a low-level enlisted man and a private contractor can steal and disclose millions of secrets, no government official can be confident that he will be able to shield his actions from public scrutiny. And while irresponsible disclosures unquestionably undermine national security, responsible leaks are an important check on secrecy’s abuse.
Snowden and Manning are only the most recent and dramatic examples. Virtually all of the most disturbing and illegal actions of the United States in its “war on terror” were authorized and carried out in secret, and only came to public attention because of leaks. Those actions included torture and cruel treatment of detainees, rendition to torture, the CIA’s “black sites,” and the NSA’s warrantless wiretapping. All of these programs were curtailed in significant part because of public pressure prompted by their disclosure. And in most instances, the leakers have not been identified or prosecuted.
In the end, the leaker puts both himself and society in a difficult position. By disclosing secrets, he may well burn his career, lose his liberty, and alter his life forever. As Snowden has said, he could have simply gone on living in Hawaii, enjoying a handsome salary in an island paradise. Instead, with considerable courage, he chose to act on his conscience, leave his country, and become an international fugitive with a future that is at best uncertain. Manning, who acted on similar motives but with less sophistication and possibly less justification, is serving a thirty-five-year sentence. Assange, who devoted himself and his website to promoting accountability through transparency, remains isolated and confined in a foreign embassy, unable to walk the streets of London (albeit, at least for the moment, for fear of facing charges of sex crimes, not prosecution for leaks).
And while we as members of the public have learned from each of these men about what our government has done behind closed doors in our name, they have also taken it upon themselves to reveal hundreds of thousands of secret documents, only some of which may have been justifiably disclosed. No one elected Snowden, Manning, or Assange to act as our conscience. But if they didn’t so act, who would?
This Issue
February 6, 2014
The Most Catastrophic War
On Breaking One’s Neck
-
1
The NSA notified members of the Senate and House intelligence committees of the program, and made some information available to other members of Congress. However, it did not disclose the questionable reasoning of the FISA courts upholding the program. The chairman of the House Intelligence Committee reportedly barred the program’s disclosure to other House members. And while senators were allowed to examine a classified letter reporting on the program, they could not bring any staff members with them, and could not take notes or copy the letter. They could review the letter only for a limited period of time, and could not discuss it with their colleagues or the public. ↩
-
2
For a discussion of Judge Leon’s ruling, see my article “The NSA on Trial,” NYRblog, December 18, 2013. ↩
-
3
Declassified Order of Foreign Intelligence Surveillance Court, March 2, 2009, at www.dni.gov/files/documents/section/pub_March%202%202009%20Order%20from%20FISC.pdf. ↩
-
4
See Barton Gellman, “Edward Snowden, After Months of NSA Revelations, Says His Mission’s Accomplished,” The Washington Post, December 23, 2013. ↩