It’s a brief window into a doomed soul. Clinging to his mother’s back, the child looks twice into the camera held by the man about to kill him. The natural curiosity of a child that fear has failed to extinguish. The smartphone captures the casual cruelty with which both mother and child are killed. Nearby, another mother and daughter are executed. One killer continues to pump bullets into the lifeless bodies with a glee that seems excessive even to his accomplices. “That’s enough, Tsanga!” one shouts. “That’s enough.”
In July 2018, when the video of the killings started circulating on social media, it was clear what had happened. The mothers and children were defenseless, they weren’t resisting, and they were killed with intent. Other facts, however, were less clear: Where did this happen, when was the video recorded, who were the killers, and why did they kill? The fact that the killers had filmed the crime suggested that they were confident in their impunity. Only precise answers to journalism’s enduring questions—what, where, when, who, and why—could revoke it.
This is the task that investigators at the BBC’s Africa Eye unit undertook over the next few months—an investigation for which they have just won a Peabody Award. Africa Eye was able to geolocate the site, matching topographical features from the video to satellite maps; establish the time, using shadows as sundials; confirm the killers’ identities, by cross-referencing social media profiles with government records; and establish that the executions were part of Cameroon’s counter-terrorism operations against the extremist group Boko Haram. Africa Eye’s findings led in February 2019 to the US’s withdrawing $17 million in funding for the Cameroonian Army and European Parliament’s passing a strong resolution condemning “torture, forced disappearances, extrajudicial killings perpetrated by governmental forces.”
The investigation was a triumph of journalism. The smartphone that had captured the victims’ last moments had turned from voyeur to witness.
Open Source Intelligence (OSINT), the method used by Africa Eye, has enabled many forensic breakthroughs in recent years. Its origins lie in the world of intelligence and law enforcement. It was the 9/11 Commission that in 2004 first recommended the creation of an open-source intelligence unit, a proposal reinforced a year later by the Iraq Intelligence Commission. But the methodology has found its most innovative and effective use in the hands of journalists.
Beginning in 2010, the open newsroom tool Storyful became a platform for collaborative investigation, laying the ground for this entirely new field of journalism. The most active and resourceful member of the original Storyful collective was the Leicester-based blogger Eliot Higgins, who developed creative new methods to crack intractable cases. Higgins’s success with open-source investigations brought him media stardom, which he used in 2014 to found Bellingcat, an international collective of researchers, investigators, and citizen journalists that conducts investigations using the techniques he had pioneered.
For much of its existence, Bellingcat has operated on a shoe-string budget, relying on the commitment and motivation of volunteers. While it received some grants from charitable foundations, its most reliable source of income was the training sessions it organized for journalists and researchers. A recent grant from the Dutch lottery fund has finally put Bellingcat in a position where it can hire a full-time staff of sixteen. Since its founding, the organization has chalked up an impressive record of breakthroughs, including valuable assistance to the BBC’s Africa Eye investigation. Its alums either lead, participate in, or support every notable open-source journalistic enterprise currently in operation.
The central pursuit in open-source investigations is finding publicly accessible data on an incident, verifying the authenticity of the data, using that data to confirm the temporal and spatial dimensions of the incident, and cross-referencing the data with other digital records. For example: on July 17, 2014, a Malaysia Airlines jet, flight MH17, was shot down over eastern Ukraine with the loss of all 298 people on board. That territory was controlled by Russian-backed separatists, and Russia was suspected of supplying a missile launcher capable of shooting down high-altitude aircraft. Moscow denied responsibility, but if the presence at the location of a Russian anti-aircraft weapon system could be proved, that would clearly undermine such a denial. Thus any photographic or video evidence of such a missile launcher near the location at the time of the crash would be damning because such missile systems are not common, and are certainly not available to non-state actors.
An open-source investigator will thus start by scouring social media for postings from the area around the time. Once such images are found, they will be geolocated using Google Earth to cross-referencing geographical features. The time for each image will then be confirmed, using digital sundials to calculate shadow length and direction. A route for the missile launcher can then be constructed by placing the photographs on a map along with the time for each sighting.
Advertisement
This is how the Bellingcat team tracked the path of a Russian Buk missile system. Using a series of images and videos that had been posted online, investigators tracked the Buk’s digital trail into and out of Ukraine. They found images of the launcher near the crash site; they even found tell-tale burn marks in a field near Pervomaiskyi, where the missile was launched; and, on the Buk’s return journey to Russia through Luhansk, they found one of its four missiles missing. It was laborious, collaborative work, with volunteers contributing from the US and Britain to Germany and Finland. The details of Bellingcat’s findings were subsequently corroborated by the Dutch-led Joint Investigation Team, comprising law enforcement officials from Australia, Belgium, Malaysia, and Ukraine.

Robin van Lonkhuijsen/AFP/Getty Images
Parts of the Buk anti-aircraft rocket that downed flight MH17 over Ukraine displayed at a news conference of the Joint Investigation Team, which confirmed Bellingcat’s conclusion that the missile launcher came from a specific brigade in Russia, Bunnik, Netherlands, May 24, 2018
Bellingcat’s successes have encouraged investment in open-source research capability by much larger and long-established media institutions (such as The New York Times Visual Investigations), human rights organizations (Amnesty’s Digital Verification Corps; Human Rights Watch’s soon-to-be-launched OSINT unit), think tanks (the Atlantic Council’s DFR Lab), and academic institutions (Berkeley’s Human Rights Investigations Lab). These efforts are part of a larger focus on information integrity called for by emerging threats to democracy and public discourse from weaponized disinformation.
This expansion of the news ecosystem is having a salutary effect on a profession in doldrums. Financial constraints have led many news organizations to downsize, leaving large gaps in foreign coverage and hollowing out investigative reporting. State and non-state actors that used to court foreign correspondents in the hopes of favorable coverage are now using the Internet to control their own narratives. Many see journalists as a nuisance or a threat. Social media chatter from foreign crises reaches audiences before it has been verified or contextualized. The pace and volume of this deluge have persuaded some newsrooms that sending journalists abroad is a fool’s errand.
With public trust in facts receding, competing narratives have come to dominate. News coverage has devolved, on one hand, into partisan hackery and, on the other, into a forced balance of “both-sides-ism.” Amid all this disarray, open-source journalism is restoring the primacy of facts and placing new emphasis on verification. It is also using digital media to cover parts of the world made inaccessible by war or distance.
A leading catalyst for the emergence of open-source journalism has been the war in Syria, perhaps the most documented conflict in history (thanks to the wide availability of smartphones). But the war has also occasioned one of the most intense disinformation campaigns. Bashar al-Assad’s regime initially tried traditional means of control, denying visas to journalists it deemed unsympathetic, targeting those who entered unauthorized. This has made independent news-gathering by foreign reporters dangerous, and citizen-sourced material has become the only alternative.
For all its utility, such material always carries the risk of inauthenticity or manipulation. With the help of its ally Russia, the regime has adapted to this new media environment by mobilizing armies of trolls to add digital noise to the mix, further diminishing trust in such material. This is where open-source verification becomes essential, establishing the authenticity of audio-visual material before any conclusions can be drawn from them.
And there is no dearth of such material. Despite crippling restrictions, even the Syrian regime’s sieges have failed to plunge rebel regions entirely into darkness. From Aleppo to Douma, millions of images and videos have emerged capturing the regime’s war crimes, providing rich material for open-source analysis. Such analysis has invariably proved accurate, inspiring enough confidence in its reliability that in 2017 the International Criminal Court issued its first indictment based primarily on open-source evidence, in this case against the Libyan warlord Mahmoud al-Werfalli.
The transparency and robustness of open-source methods is encouraging greater resourcefulness and rigor even among traditional journalists. It has certainly exposed the inadequacy of the approach used by some celebrated journalists who, in recent years, have turned out to be vessels for disinformation. It is also a departure from the “transparency revolution” of the past decade when platforms like WikiLeaks were able to build reputations on the credibility and impact of their leaks while remaining opaque about their process and motivations. They transferred the risks of leaking and the consequences of publishing to others. By contrast, leading open-source practitioners have built their reputations by being transparent about their methods and responsible with their data.
Advertisement
Part of open-source journalism’s new-found cachet comes from its methodological sophistication, but much of its credibility derives from its transparency. Recent OSINT-based journalism achievements—such as Bellingcat’s investigations into the downing of the Malaysian airliner MH17 and the Skripal poisoning; The New York Times’s investigations into the killing of the Gaza medic Rouzan al-Najjar and identifying the killers of Jamal Khashoggi; Africa Eye’s work on the Cameroon killings; DFRLab’s work on Twitter trolls; and UC Berkeley Human Rights Center’s contribution to Reuters’s Pulitzer Prize-winning investigation in Myanmar—are compelling not just for their findings, but for the openness with which they explain the process of discovery.
This is the closest that journalism has come to a scientific method: the transparency allows the process to be replicated, the underlying data to be examined, and the conclusions to be tested by others. This is worlds apart from the journalism of assertion that demands trust in expert authority.
Many media commentators and news consumers have welcomed this development. But some traditionalists remain unimpressed. It’s their criticism, however, that offers inadvertent testimony to the value of open-source journalism, especially when contrasted with their own methods.
The Pulitzer Prize-winning journalist Seymour Hersh, for example, has been dismissive of open-source investigations. It was the August 21, 2013, chemical attack on Ghouta, Syria, that first put them at odds. Eliot Higgins, then running an obscure blog named Brown Moses, had quickly gathered data from YouTube videos, satellite imagery, and UN reports to verify the dimensions of the munitions used in the attack and confirm their make and likely trajectory. The rockets matched a model in the regime’s arsenal and the trajectory could be traced back to regime-held territory.
Months later, Hersh published a long story in the London Review of Books claiming that the Obama administration had manipulated evidence and colluded in a false-flag operation to implicate the Syrian regime of President Assad. In making this incendiary claim, Hersh relied on the testimony of an unnamed “former senior intelligence official.” Although central claims in Hersh’s story were soon challenged, he simply redoubled his efforts and published an even longer version, also published by the London Review of Books. That trusty warhorse the “former intelligence official” told Hersh: “We now know it was a covert action planned by [Turkish President Recep] Erdoğan’s people to push Obama over the red line.”
Hersh was demanding the reader’s trust while relying on a single anonymous source whose credibility he could not establish, citing documents he hadn’t seen, making allegations he could not substantiate. He also failed to acknowledge extant evidence that contradicted his story. Higgins, on the other hand, had relied on verifiable data and a robust method to prove beyond doubt that the rockets were of a manufacture used by the Syrian regime and that their trajectory placed their provenance in government-controlled territory. For Hersh’s story to be true, not only did everyone else have to be wrong, they also had to be colluding (since they had all independently reached the same conclusion about the attack); Higgins’s analysis, on the other hand, was based on accessible information and supported by physical evidence, witnesses on the ground, as well as numerous international observers and institutions, including the UN, human rights groups, and the US, British, German, and French governments.
The cycle repeated in April 2017, after the Syrian regime launched another chemical attack on the town of Khan Shaykhun (sometimes also spelled Sheikhoun). Hersh presented an alternative narrative that relied on an unnamed “senior adviser to the US intelligence community,” but he got the time of the attack wrong, could not identify the location, and seemed oblivious of the fact that the impact site bore no resemblance to the scene he described. A comprehensive investigation by the UN-OPCW Joint Investigative Mechanism would corroborate the details of Bellingcat’s open-source analysis, leaving Hersh and his German publishers humiliated. (On this occasion, after the LRB declined to publish his story, Hersh had turned to the German conservative daily Die Welt.) Although Russia had restricted the OPCW’s remit to prevent it from identifying the perpetrator, the UN researchers later confirmed to Reuters that the sarin gas used in August 2013 came from the same regime stock used in Khan Shaykhun.
James Harkin, the director of the London-based Center for Investigative Journalism, is also a skeptic. In an article for The Intercept in February, he noted that open-source investigations may be an “exciting reporting tool,” but the “photos, video, and social media posts” offer “a vanishingly narrow, excoriatingly subjective view of how conflicts unfold.” He stressed the need for fighting electronic noise and warned that without investigative journalists, “the next world war might begin with a grainy, contested image launched online from some distant and inaccessible outpost.”
Harkin’s critique is odd since one of the great values of open-source investigations is in determining the authenticity and provenance of contested images. Open-source analysts are acutely aware of the risk of manipulation. Advances in image-capture technologies still lag behind advances in image manipulation, and with the advent of “deepfakes”—an advanced form of video manipulation that maps one person’s features onto a source image, allowing the latter to speak through a realistic digital mask—verifying audio-visual material is likely to become harder. Mindful of these risks, open-source researchers take a “foundationalist” approach, verifying and geolocating audio-visual data before drawing any larger conclusions from them.
Within weeks of the April 2018 chemical attack on Douma, Syria, an investigation by The New York Times in collaboration with Bellingcat and Forensic Architecture had established where the attack was, when it happened, who carried it out, and what weapon was used. Harkin spent months investigating the story, even visiting Douma (albeit with a “minder-translator” provided by the regime); and while his findings broadly supported The New York Times’s, Harkin chose to include testimonies from people living under regime authority who denied that a chemical attack had taken place. When the OPCW published its comprehensive report, a year after the attack, it fully corroborated the Times/Bellingcat analysis.
Distance, it seemed, was no barrier to a robust investigation and proximity was no guarantee of clarity. What mattered was the credibility of the sources. In the case of the Times, this was easy to establish since it relied on publicly accessible data. The credibility of Harkin’s sources was harder to establish.
The remoteness of open-source analysts from the subject of their analysis is not as absolute as its critics make it out to be. Much of the data used in open-source analysis comes from witnesses on the ground who have more immediate access to events. The ubiquity of smartphones with high-quality cameras means that every newsworthy incident has potential witnesses with the ability to document it. Nor is it accurate to say that people living under siege or under an authoritarian regime are electronically inaccessible; even China can’t enforce that level of control. The risks are certainly greater, but citizen journalists in Syria, for example, have been able to upload texts, images, and videos not just from rebel areas, but also from territory under regime or ISIS control.
All of this is particularly welcome for human rights and war crimes monitors. The obsessive commitment of open-source investigators means that they remain focused on a story long after it has dropped out of the headlines. And in this new global panopticon, there are few significant events that escape a camera’s eye: according to the Pew Research Center, some 5 billion people worldwide own mobile phones, half of them equipped with cameras. Victims, witnesses, even perpetrators can all document crimes. Subjective experiences are thus added to an objective world of factuality, available for any researcher to verify and analyze. Though powerful states have tried to restrict electronic communications, information has so far always found a way to escape.
Consider the case of Bana al-Abed, a then seven-year-old girl, who, with the help of her mother, was live-tweeting from the besieged Syrian city of Aleppo in 2016. Her story about the horrors of life under siege and bombardment drew attention to the plight of the people trapped in Aleppo. The regime, the Russian media, and their online supporters responded by threatening, trolling, mocking, and harassing the child, alternately claiming that she didn’t exist or that she was a fabricated avatar for a jihadist-friendly PR operation run out of Turkey. Nick Waters, a former British Army infantry officer working with Bellingcat, used images and videos Bana had posted online to establish who she was, where she lived, and how she accessed the Internet. Knowing the threat Bana was under, though, Waters and Bellingcat withheld the information until she and her family were safely evacuated by the Red Crescent. Instead of pursuing a scoop, Bellingcat recognized the obligation to protect the subject of its investigation—in stark contrast to the approach taken by WikiLeaks in publishing unredacted documents without regard to their potential impact on people’s lives.
That voluntary adherence to such a protocol is all the more remarkable since there are no professional guidelines regulating this sphere. Most open-source investigators aren’t formally employed as journalists—some emerged from a gaming subculture where street cred derives from the economy and precision of one’s method—and professionals from other fields of expertise such as architecture, medicine, chemistry, finance, and law have found uses for their specialist knowledge in unraveling forensic puzzles. The British-Israeli architect Eyal Weizman has pioneered the entirely new field of forensic architecture, using open-source data for spatial investigations into human rights violations; the chemical weapons expert Dan Kaszeta has contributed to several Bellingcat investigations; UC Berkeley’s Human Rights Investigations Lab recruits from over a dozen disciplines.
Open-source analysis can have its limitations. It is at its best when it confines itself to addressing factual questions, but it can fall into error if it starts offering inductive judgments based on the data that is available without being sufficiently mindful of what data may be missing.
The New America Foundation, for example, produced widely cited statistics on drone strikes during the Obama era that were culled from published media reports.
However, these statistics ignored the fact that the reporting on drone strikes was sporadic and casualty figures were drawn from official claims without any on-the-ground verification. Predictably, this led to the undercounting of civilian casualties. (The perils of such “passive surveillance” were illustrated in a different theater when Azmat Khan and Anand Gopal conducted a year-long investigation for The New York Times into the US-led coalition’s anti-ISIS campaign in Iraq that revealed that civilian casualties occurred in 20 percent of airstrikes, a rate more than thirty-one times higher than the Pentagon was reporting.) A more rigorous method was eventually developed by the journalist Chris Woods of the Bureau of Investigative Journalism that combined media reports with independent corroboration to produce more reliable casualty figures. Wood now runs the independent Airwars.org, which gathers open-source data to monitor the airstrikes in the US-backed coalition’s anti-ISIS operations in Iraq and Syria.
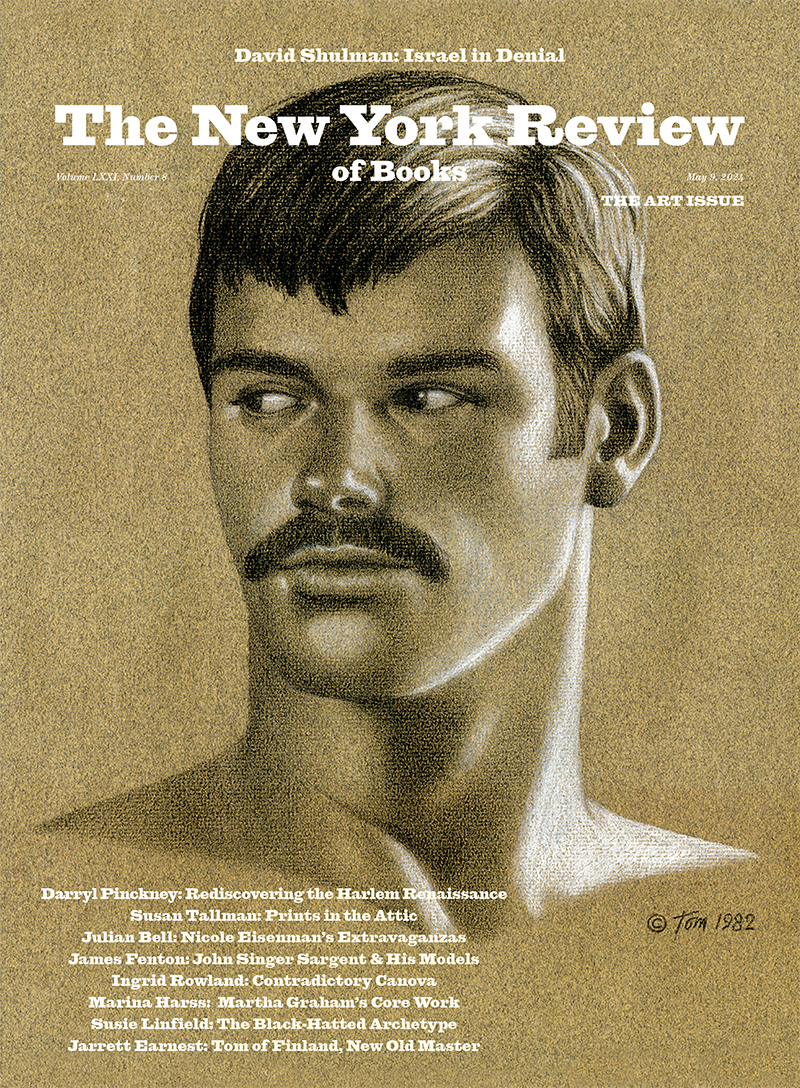
In the years to come, responsible publishers will have to invest in greater capacity for robust fact-checking and digital verification—and only media giants like the Times or the BBC have the resources to maintain fully-staffed open-source investigations units. Meanwhile, dedicated organizations like Bellingcat will continue to produce the bulk of such analysis. As a recent documentary by the Dutch broadcaster VPRO, Bellingcat: Truth in a Post-Truth World, has revealed, this model of small independents operating without large institutional backing can leave their researchers exposed when taking on the interests of state actors as ruthless as the Kremlin or the Saudi regime.
For all the current nostalgia about the Times’s reporting on the Pentagon Papers or The Washington Post’s pursuit of Watergate, it is probably true to say that journalism never had a golden age. Instead, the business of news-gathering finds itself in the middle of an institutional and epistemic crisis—one that can only be solved by an unflinching commitment to truth and accuracy. Open-source journalism is here not to replace traditional journalism but to reinforce it. It does so by never taking its readers’ trust for granted; it earns that trust only by delivering rigor and transparency. In contrast to the competitive ethos of traditional journalism, the OSINT approach is cooperative, a form of socially distributed cognition that draws expertise from any relevant discipline for the best possible results. Journalism badly needs this infusion of vitality and credibility.